Set up PuTTY
To set up the SSH tunnel, we will be using the excellent PuTTY client. We will be using the Portable version of PuTTY, a release packaged by the folks over at Portableapps.com.
Run the installer to load PuTTY onto your USB drive. Start PuttyPortable.exe. The next step is to set up the SSH connection and tunnel.
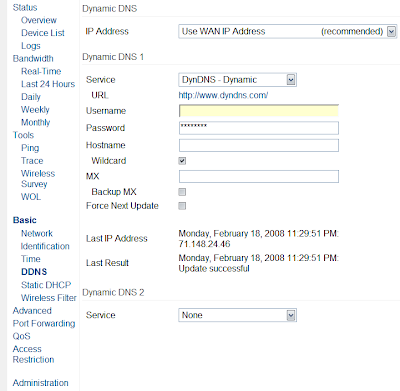
The first step is to enter the address of your router (the DynDNS address mentioned in Part 1). Ensure that the protocol type is SSH, and make sure you change the port number to 443.
The next step is to set up the dynamic SOCKS tunnel. Go to the Connection->SSH->Tunnels menu. In the source port box, specify a port greater than 1024 (<1024 style="font-weight: bold;">"Dynamic" radio button. Finally, click Add. The tunnels screen should look something like this when finished:
Now go back to the main screen (see first screenshot). You probably want to save the current settings as a profile - this allows quick connections in the future.
With everything set up, it is time to connect. Hit the Open button at the bottom of the PuTTY dialog. You should be greeted with a terminal window now - type in the router's username and password as requested. A successful connection should look similar to this:
Leave this open as long as you want to use the tunnel. Type exit when finished.
Set up applications to use the tunnel
Well, you ask, how do I actually start tunneling things through? The tunnel you created is basically a SOCKS proxy. SOCKS is a protocol for proxying just about any type of data. Many applications support communicating through a SOCKS proxy (Firefox, Pidgin, etc.)
Use the following values when configuring applications to use the tunnel:
- Proxy type: SOCKS 4/5 (if you mistakenly select another protocol, such as HTTP, IT WON'T WORK!!!)
- Proxy address: localhost (or the loopback IP address 127.0.0.1)
- Proxy port: whatever you chose as the tunnel's port number in PuTTY)
Load Up Your USB Drive with Apps
For even more convenience, it is a good idea to put some additional programs on your USB drive that can take advantage of the SSH tunnel. For example, I currently have Portable Firefox on my USB drive, complete with the FoxyProxy extension for easy, on-the-fly switching between direct connect mode and SSH tunnel mode. This makes web browsing and bypassing filters a snap - I just plug it in and go, with the added bonus of a fully customized Firefox environment, with my bookmarks and homepages all right there. I also have the Pidgin IM client installed on my drive - see this page for more details on enabling its portable function.
With the SSH tunnel, you will be able to securely use any protocol and any application, as long as it supports the use of SOCKS. The freedom of the web is awaiting...and as an added bonus, no one will be the wiser to your encrypted activities.