I'm writing this post in a dorm room at Northwestern University, where I've been for almost two weeks. I am taking AP Computer Science A through Northwestern's Center for Talent Development (CTD)- a fancy name for what is more or less a summer camp.
But enough of that. As with my earlier post about the University of Chicago, I'm going to highlight some of my personal observations and experiences while on campus. I wish I had some pictures to share, but unfortunately I don't have a camera handy...

Academics
I can't really provide a true impression of Northwestern's academic programs, as CTD is a high school program. The teachers are predominantly from high schools near Evanston. Of course, this does not imply anything about their level of knowledge. In terms of the actual college, though, Northwestern is highly regarded, particularly the journalism and business programs. Naturally, admissions are competitive, with a 26% admissions rate. Here are some ACT/SAT stats, courtesy of the College Board:
| | Middle 50% |
| SAT Critical Reading | 670 - 750 |
| SAT Math | 680 - 770 |
| SAT Writing | 660 - 750 |
| ACT Composite | 30 - 34 |
Obviously, these are some high-powered scores. Personally, though, I have little to worry about in the standardized test department! :D
Campus, Housing and Location
Northwestern University is located in Evanston, IL, only about 15-20 minutes away from Chicago. Simply drive north on Lake Shore Drive, and you'll reach Evanston pretty quickly. The nice thing about Evanston is that it is a good-sized city (population 74,000) with all the resources one would want, but is right next door to the Windy City. Evanston is a decent place, with a combination of urban and suburban life, but it also has its seedier places. Transportation is a cinch since the CTA Purple Line lightrail system runs through.
The Northwestern campus is well-regarded for its scenic beauty, and I can see why. All of the old buildings are built of a pleasing beige-colored stone, and ivy is abundant. The Norris University Center, a looming multilevel structure, is a bustling hub of students, food, and activities. Our Comp Sci classroom is located in Annenberg Hall, a newer building with computer labs and tech-heavy classrooms.
My dorm, Allison Hall, has definitely seen better days; the ivy and surrounding trees, though, somewhat compensate for that. Currently, there is a lot of construction going on, marring the landscape. Each double room has two desks, a bunk bed, and a retrofitted window air conditioner. The bathrooms have an odd smell, no thanks to their constant use over the years by some (not-so-clean) students. There are dual Ethernet lines in each room running at 10Mbps (a holdover from a previous era?) Obviously, Allison can't hold a candle to the brand-spankin' newness of Max Palevsky Commons over at the University of Chicago, but it's still a fun and lively place to be.

the famous Northwestern arch
Food
As residential students we're entitled to three meals a day. The food service definitely has its on and off days. Some days, their is a reasonable variety of food - mac and cheese, fries, pasta, rice, fruit - while other days there is almost nothing except for excessively greasy burgers. Breakfast blows all the time, though because they always seem to serve the same old menu of scrambled eggs and French toast. Nevertheless, I'm grateful for the soda machines, which are on during every meal - perfect for grabbing a drink to go.
Naturally, an escapade to restaurants to town is a must when the in-house dining is deficient. There are many choices - Chipotle, Potbelly, Flat Top Grill, pizza, Joy Yee's Noodles, and various chicken places.
Student Life
A school can often be judged by the quality of its students.
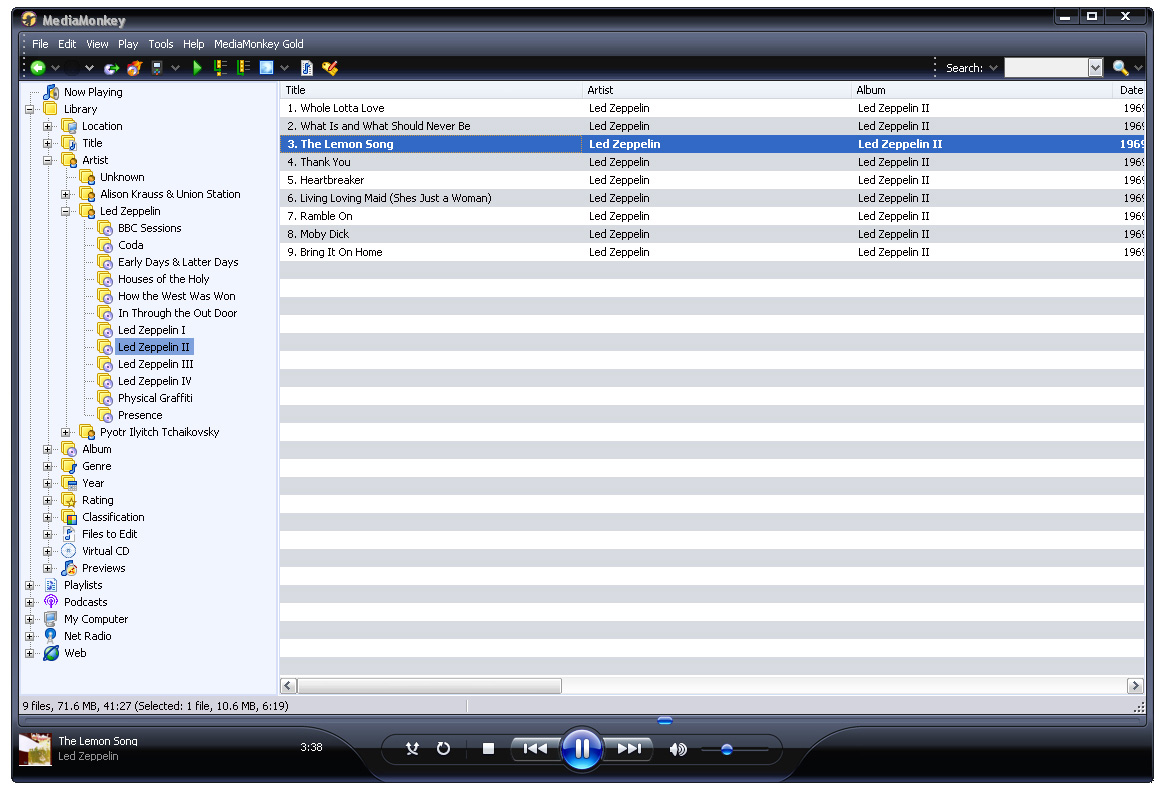
Here at CTD,  most of the kids are pretty well-equipped in the brain department. Not surprisingly, our Comp Sci class has a highly skewed male:female ratio (guess in which direction?) Diversity is abundant: many of the kids come from neighboring states, while others come from across the country or even internationally (Korea). Many of us are quite quirky and have exotic interests (chess grandmaster, anyone? or one of the best Quiz Bowlers in the nation?) The residential teaching assistants are equally interesting - hardcore gamers, med school students...you name it.
most of the kids are pretty well-equipped in the brain department. Not surprisingly, our Comp Sci class has a highly skewed male:female ratio (guess in which direction?) Diversity is abundant: many of the kids come from neighboring states, while others come from across the country or even internationally (Korea). Many of us are quite quirky and have exotic interests (chess grandmaster, anyone? or one of the best Quiz Bowlers in the nation?) The residential teaching assistants are equally interesting - hardcore gamers, med school students...you name it.
Conclusion
Northwestern University, is, simply put, an awesome institution. From the life to the students, it's a decent school that caters to an entire spectrum of people and tastes. The lush campus and surrounding town supplement the academic reputation. Northwestern University is definitely on my Common App's list of schools...













 On Friday, we took the
On Friday, we took the  this time to see (and taste?) the
this time to see (and taste?) the  festivities at Millennium Park. After a quick drive down to the Metra station, we hopped on and got off at Van Buren Street. The place was crawling with cops - near the subway station, their was a crapload of cop cars, cop SUVs, and unmarked police vehicles. Downtown, there were at least two cops on every street corner. After stops at Chipotle and Jamba Juice, we headed for Millennium Park. Getting there meant (at least, according to my roommate's dad) a little shortcut through the Taste of Chicago grounds. Unfortunately, our plans were ruined by the crowds there, which were even worse this time around. By the time we escaped, it was already too late and we had to go back for curfew. But, at the very least, we had enough crowds for a lifetime.
festivities at Millennium Park. After a quick drive down to the Metra station, we hopped on and got off at Van Buren Street. The place was crawling with cops - near the subway station, their was a crapload of cop cars, cop SUVs, and unmarked police vehicles. Downtown, there were at least two cops on every street corner. After stops at Chipotle and Jamba Juice, we headed for Millennium Park. Getting there meant (at least, according to my roommate's dad) a little shortcut through the Taste of Chicago grounds. Unfortunately, our plans were ruined by the crowds there, which were even worse this time around. By the time we escaped, it was already too late and we had to go back for curfew. But, at the very least, we had enough crowds for a lifetime.