Back in Part I of the tutorial, I covered the process of creating an image of a Linux computer (running Fedora) using FSArchiver and an external USB hard disk as the backup medium. Now, we’re going to restore the image onto a target computer (with a different hardware configuration) and prep this new system for booting. Our goal: That the target machine will run a Linux environment that appears virtually identical to the user, thus saving lots of time that would otherwise be needed to reinstall software, tweak the user environment, etc.
Create partitions
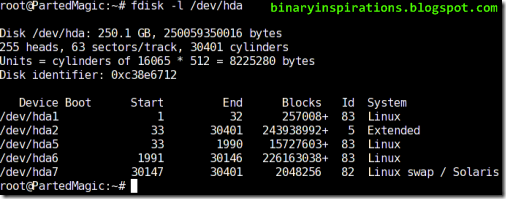
In order for the cloning to work successfully, you will need the same number of partitions as on the source machine, plus an optional swap partition. Each partition, in turn, must be large enough to store all of the data that will be restored onto the partition. Parted Magic, true to its name, provides the excellent and easy-to-use GParted tool, a GUI frontend to the parted partitioning software. The nuts and bolts of using GParted are out of the scope of this article; please see the official documentation for more details.

In the example screenshot above, I have created several partitions on a WD10EADS 1TB hard drive. /dev/sda3 is a 200MB /boot partition. Furthermore, /dev/sda4 is an extended partition that contains the / root partition /dev/sda5, the large /home partition /dev/sda6, and the swap partition /dev/sda7 (again, swap is optional. It is more relevant to low-RAM systems). Note that formatting the partitions (with the exception of swap, if you created one) is not necessary, since FSArchiver will format each partition to match the parameters of the source filesystem.
Mount the backup medium and restore the image
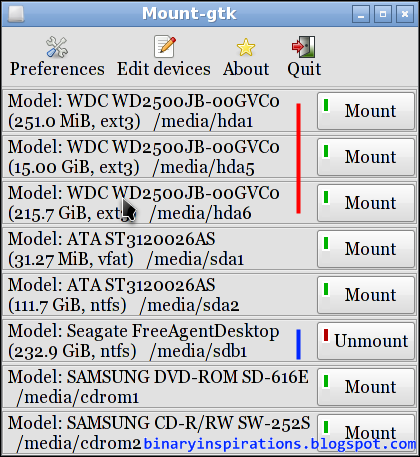
Now it’s time to restore the image onto the new partitions. Run the mount manager and mount your external disk.

In the example above, I have mounted my Seagate drive, /media/sdc1.
After mounting the image, open a terminal prompt and cd to the mount point of the external disk, e.g. /media/sdc1. To execute the restore process:
# fsarchiver restfs –v /media/XYZ/ARCHIVE_NAME.fsa id=0,dest=/dev/X1 id=1,dest=/dev/X2,id=2,dest=/dev/X3
Replace with the correct parameters relative to your particular system, of course. You can also add a –j X, where X is the number of processor cores available, to enable multithreading. Make sure the partitions you are restoring to correspond to the order of the partitions in the image file. The restore process make take anywhere from a half hour to several hours or more, depending on your CPU speed and hard drive.
Fix the GRUB bootloader
Next, we need to ensure that the grub.conf file points to the correct partitions. Mount your boot partition and go to grub/grub.conf. Make sure that the splashimage and root of each boot entry points to the proper partition. Keep in mind that grub starts counting from 0 – so if you have a partition /dev/sda3, it would be known as (hd0,2). Likewise, /dev/sdb1 would be (hd1,0).
Now that our grub.conf is correct, we need to install GRUB on the MBR (master boot record) of your primary (boot) hard drive. Determine what your boot partition is using the guidelines in the previous paragraph. Let’s say my boot partition is (hd0,1). Then my commands would be:
# grub
grub> root (hd0,1)
grub> setup (hd0)
At this point, your system is ready to boot into its new, cloned Linux environment. Yes, it can boot – but will most likely fail. This leads us into the final steps…
Rebuild the initrd
The initrd is the Linux Initial Ramdisk, a sort of early boot environment that prepares the root environment for mounting later on in the booting process. During a regular (e.g. from the install CD/DVD) Fedora installation, the installer generates a ramdisk specific to the computer’s disk and hardware setup. Since the whole point of this tutorial is that we are assuming a different set of hardware, the original initrd image is useless.
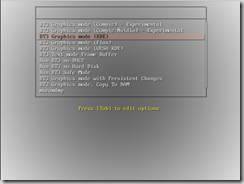
First, we need to find the version string for the kernel on the system. On a running system we could just do a uname –a, but since we’re running off a LiveCD this won’t work. An alternative would be to check grub.conf. A typical kernel version string would be something like:
2.6.29.6-217.2.16.fc11.i686.PAE
Generating a new initrd can be a bit tricky, depending on whether you have a separate boot partition or a unified / partition with a boot directory.
The latter situation (a single, unified root+boot partition) is fairly straightforward. Using the mount manager, mount this partition and note its mount point. Open a command prompt:
# chroot /media/XYZ (replace XYZ with the appropriate location)
# cd boot
# mkinitrd –f initrd-KERNEL_VERSION_STRING.img KERNEL_VERSION_STRING
Obviously, replace KERNEL_VERSION_STRING in the last command with the kernel string specific to your Linux image. This command will overwrite any existing initrd image for that version of the kernel.
The former situation, involving separate / and /boot partitions, is slightly more tricky. The basic idea is the same; however, since a chroot is involved we cannot run mkinitrd and tell it to write across partitions. One way to overcome this is to mount both partitions, write the initrd file to the / filesystem, and move (mv) it where it belongs to the boot partition. Another, slightly more advanced method is to first mount the / partition, then mount the boot partition to the /boot directory on /.
Setting up swap space (optional)
If you created a swap partition, you’ll need to let the computer know about it. First, we’ll need the UUID of the swap partition. To do this, run:
# blkid
Note the device mapping and UUID (in quotation marks) of the swap partition.
Now mount the / partition and go to etc/fstab. Edit, or create if necessary a line like the one below, making sure to use the UUID from blkid:
UUID=c2f72258-bcd7-4cff-93fc-e584bb03226f swap swap defaults 0 0
A Few Last Tweaks
There are a few more tweaks that I highly recommend. On the cloned / partition, edit the file etc/udev/rules.d/70-persistent-net.rules and delete all lines beginning with “SUBSYSTEM”. This will force the Linux install to redetect the computer’s network hardware.
Finally, make sure your video settings will work with the new machine. Recent versions of X (like that shipped with Fedora 11) do not require an /etc/X11/xorg.conf file, but if you have installed either the ATI or nVIDIA proprietary drivers, make sure that the hardware in your computer is compatible. If in doubt, simply delete the aforementioned xorg.conf file to allow X to autodetect your video hardware and select a generic driver.
Congratulations! At this point, your Linux clone is fully prepared and ready to run. Reboot from Parted Magic and cross your fingers – you should see a nice GRUB bootscreen IDENTICAL in appearance to the one on your original computer. Boot as usual, and you should experience a user interface that’s exactly the same as the way you left it. Enjoy your new old system!